Follow Us:
P.O. Box 3, Wollaston MA 02170
Email: info@databoiler.com



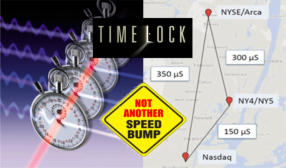
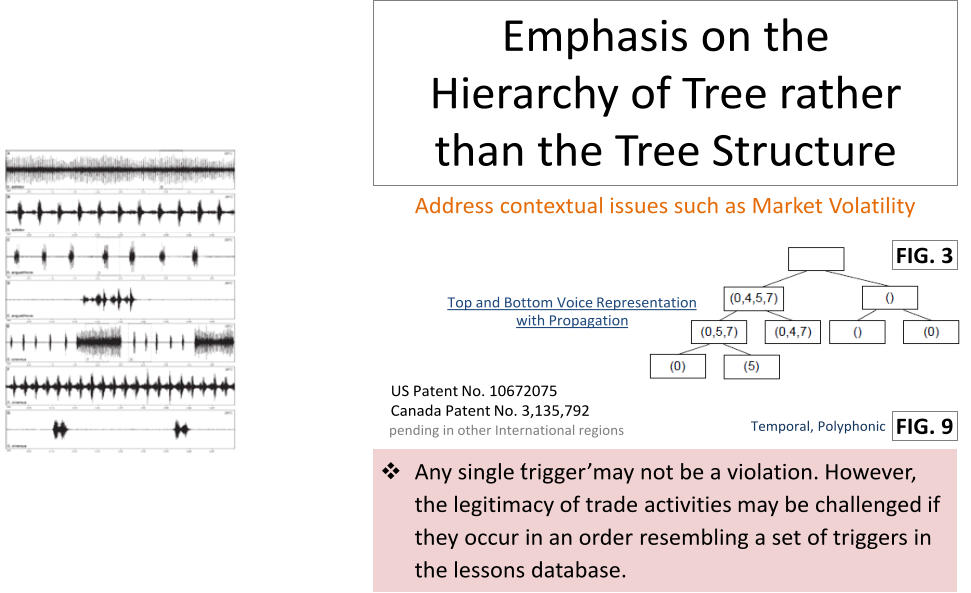
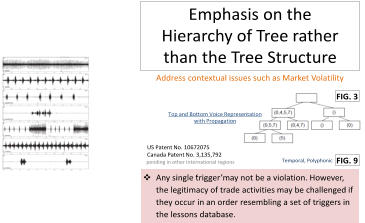
Patented solutions that crossover between music and trade provide more accurate detection of onset signals / trade
irregularities at accelerated speed and more tolerable to unsynchronized clocks/ timestamp issues + more.
•
The ONLY solution to address IOSCO - CR12/2012 challenges to effective market surveillance
•
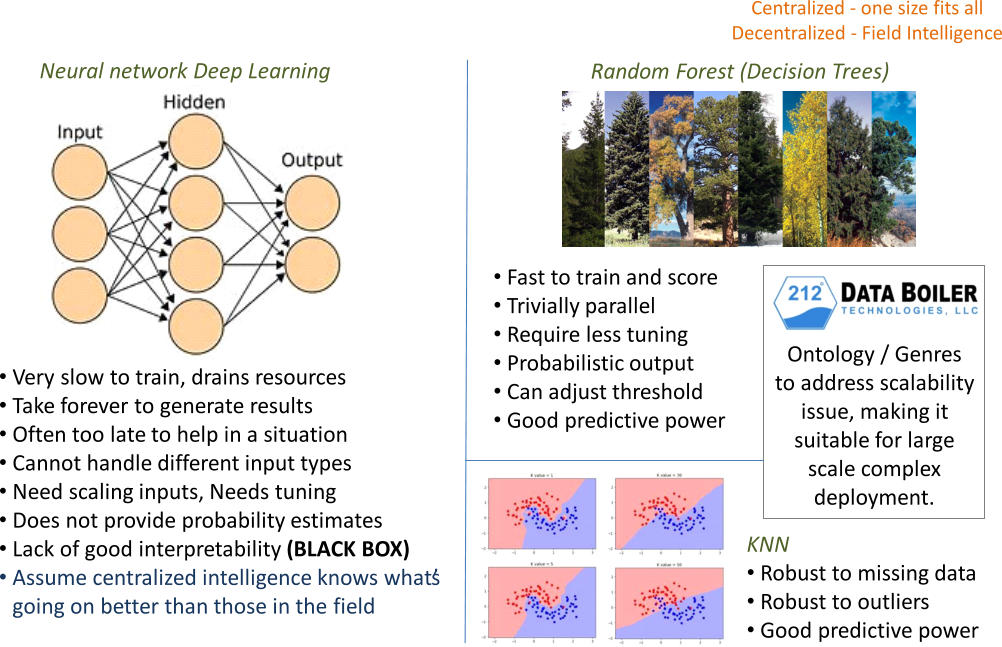
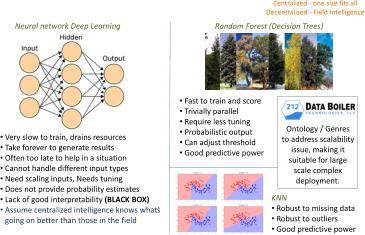
Machine learning, ontology to enable algos development and discovery of unknowns without the expensive and hard-to-learn tools
•
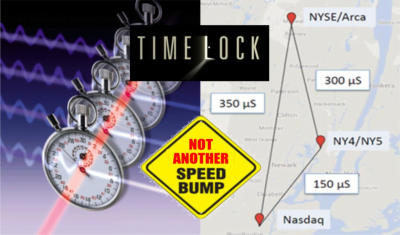
Time-lock cryptography to make market data available securely in synchronized time
Applicable to all trading desks, cross-asset classes, and markets
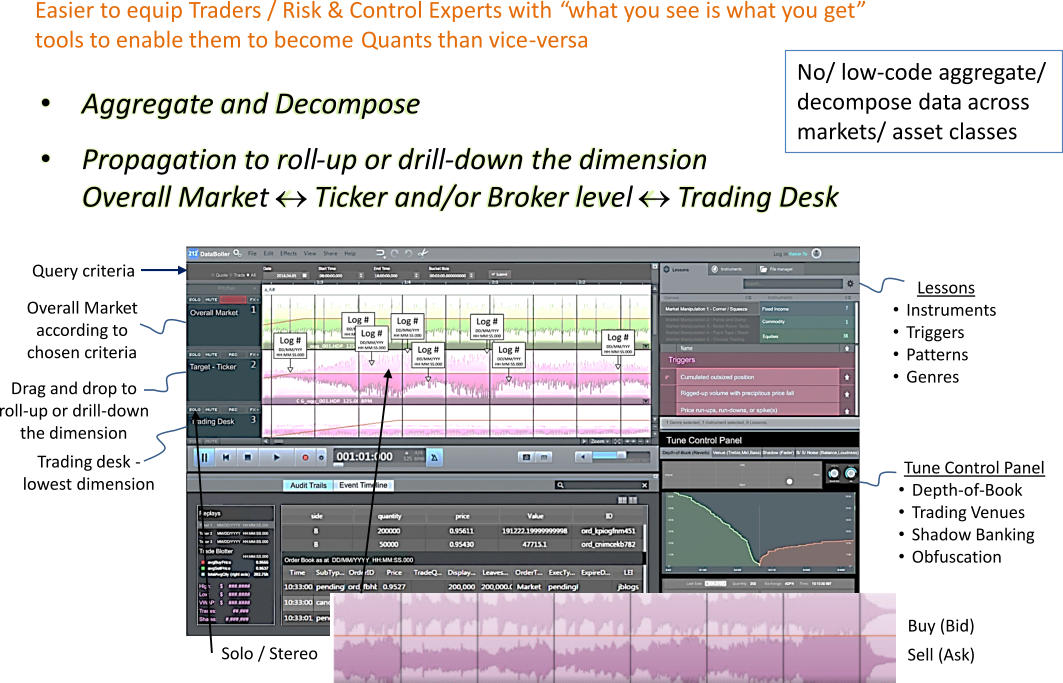
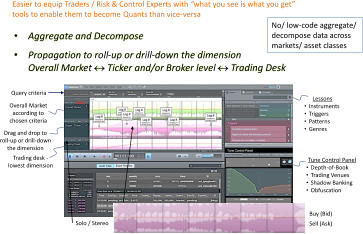
Our patented solution reduces data storage and boosts the efficiency in data distribution, while also enabling the replicate the depth-of-book
information (relative strengths in bid/ask price and steepness of the price curve). We acknowledge that the buy-side also wants the SIP to include all
the odd-lot details amid some hidden cost for high priced stocks. Our response is: When we are in the midst of systemic reform, asking for too much
or insisting on “complete” transparency, may indeed be detrimental to price discovery and the sustainable development of a healthy market. We do
want to strike the appropriate balance to avoid a “No fish can survive when the water is too clear” situation. Given that, we’ll preserve the richness of
contents the best we can, while making the tools fast, easy, secure, and fit for the effective monitoring of trade activities.
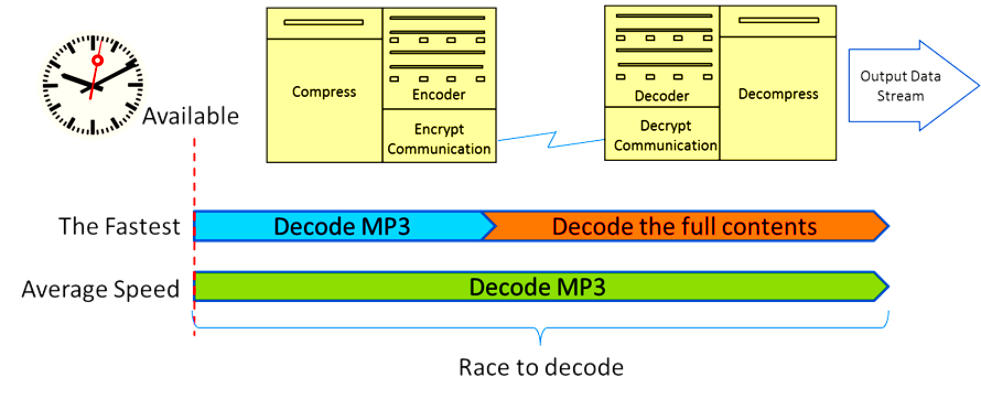
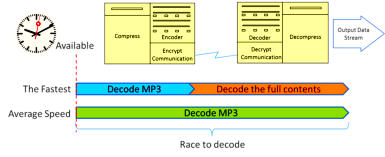
MP3 is indeed a lossy compression type, while human ears cannot distinguish almost any difference from lossless music. Lossy methods yield a
substantially greater compression ratio (60% or more of the original stream) as compared to traditional techniques (only 5-20%) that exploit statistical
redundancy, Huffman coding, or probability method to represent and compress market data.
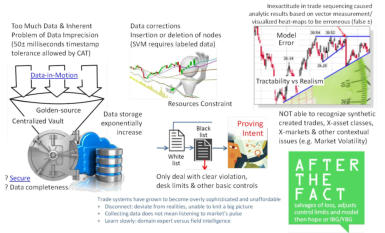
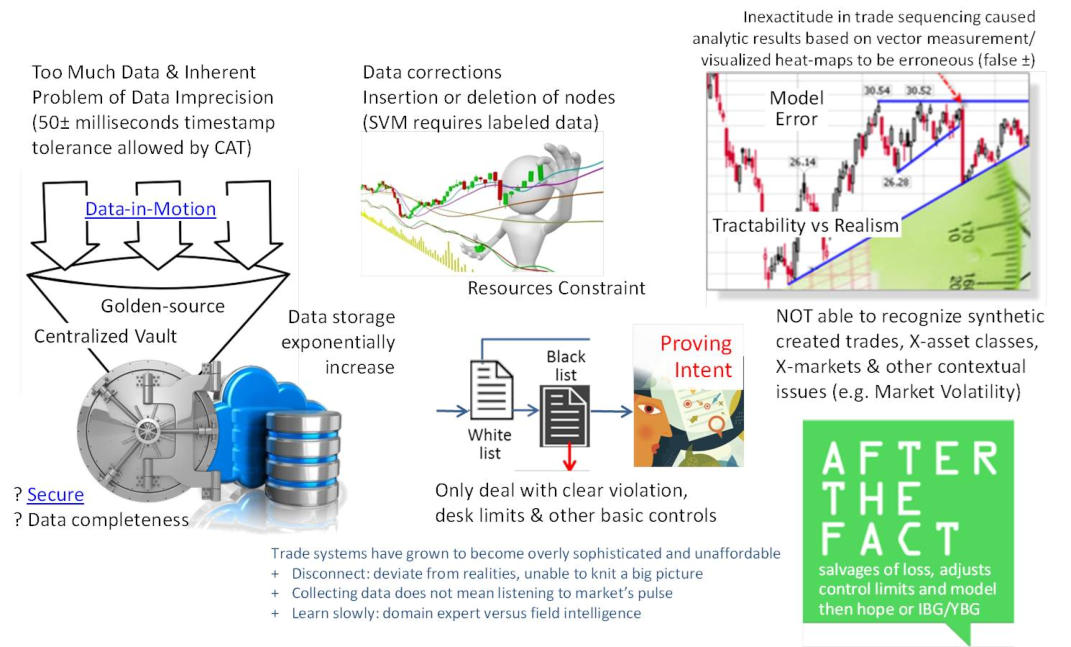
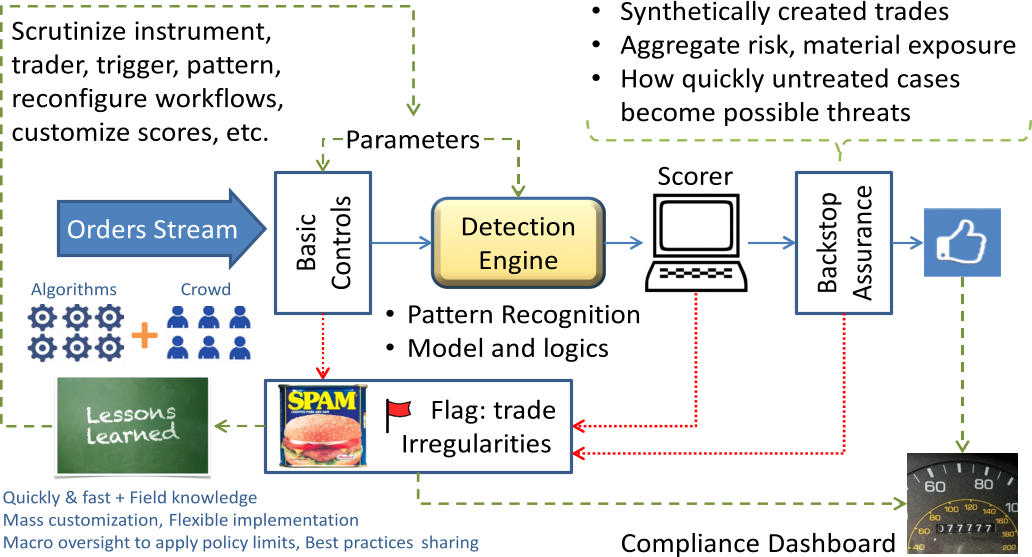
Since a thousand trades can occur between 50 +/- milliseconds, the inexactitude in trade sequencing would cause analytic results based on vector
measurements/ visualized heat-maps to be erroneous. To overcome this inherent problem of data imprecision, our suite of patented inventions
applies a “music plagiarism detection” method to achieve higher tolerance to the unsynchronized clock issue and is capable of recognizing patterns
more quickly (up to 50 milliseconds top speed, as compared to taking hours or days or even months for trade review). Aside from the accelerated
speed to decipher what’s going on in the market, it has fewer false-positives/ false-negatives than the traditional techniques. It makes
implementation of preventive controls in real- time possible; and there are other benefits such as the ease of trade reconstruction, order book replay
simulation, backstop assurance, case management capabilities, crowd computing methods, and more.

Context of the Problem
Different Learning Models


DEMO
Dectection Engine
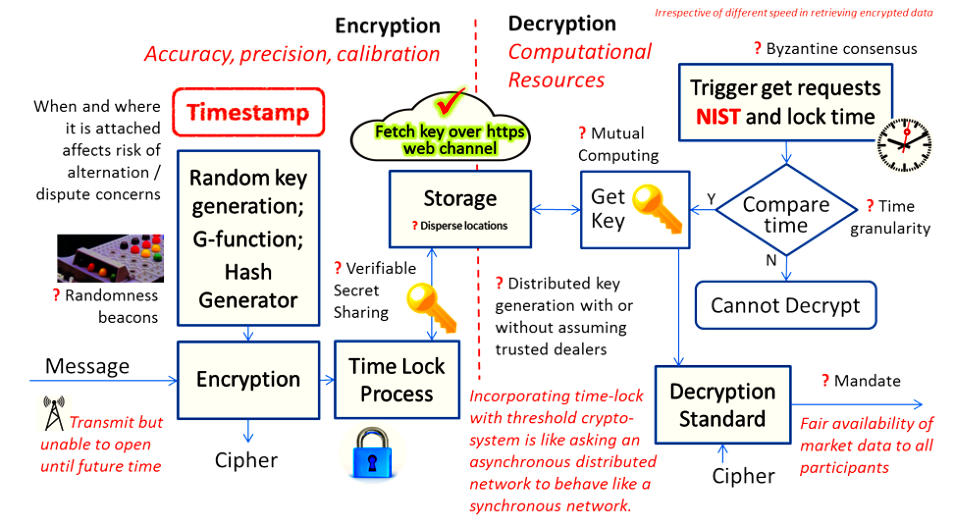
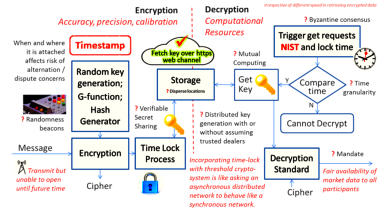
Time-lock encryption is a method to encrypt data such that it can only be decrypted after a certain deadline has passed. The goal is to protect data
from being decrypted prematurely. There are various ways to build time-lock encryption for different protection requirements. The architecture needs
precise calibration of time with an independent time aware atomic clock, such as the NIST. Besides, we don’t want to push the bottleneck to an
arms-race of using high-performing computers to decrypt data. Hence, computational resources and the type of data content must also be
considered in the design of a reliable encryption scheme.



Follow Us:
P.O. Box 3, Wollaston, MA 02170
Email: info@databoiler.com




Patented solutions that crossover
between music and trade provide more
accurate detection of onset signals /
trade irregularities at accelerated speed
and more tolerable to unsynchronized
clocks/ timestamp issues + more.
•
The ONLY solution to address IOSCO -
CR12/2012 challenges to effective market
surveillance
•
Machine learning, ontology to enable algos
development and discovery of unknowns
without the expensive and hard-to-learn tools
•
Time-lock cryptography to make market data
available securely in synchronized time
Applicable to all trading desks, cross-asset
classes, and markets
Context of the Problem
Different Learning Models


DEMO

Time-lock encryption is a method to encrypt data
such that it can only be decrypted after a certain
deadline has passed. The goal is to protect data
from being decrypted prematurely. There are
various ways to build time-lock encryption for
different protection requirements. The architecture
needs precise calibration of time with an
independent time aware atomic clock, such as the
NIST. Besides, we don’t want to push the
bottleneck to an arms-race of using high-
performing computers to decrypt data. Hence,
computational resources and the type of data
content must also be considered in the design of a
reliable encryption scheme.
Our patented solution reduces data storage and
boosts the efficiency in data distribution, while
also enabling the replicate the depth-of-book
information (relative strengths in bid/ask price
and steepness of the price curve). We
acknowledge that the buy-side also wants the
SIP to include all the odd-lot details amid some
hidden cost for high priced stocks. Our response
is: When we are in the midst of systemic reform,
asking for too much or insisting on “complete”
transparency, may indeed be detrimental to price
discovery and the sustainable development of a
healthy market. We do want to strike the
appropriate balance to avoid a “No fish can
survive when the water is too clear” situation.
Given that, we’ll preserve the richness of
contents the best we can, while making the tools
fast, easy, secure, and fit for the effective
monitoring of trade activities.
MP3 is indeed a lossy compression type, while
human ears cannot distinguish almost any
difference from lossless music. Lossy methods
yield a substantially greater compression ratio
(60% or more of the original stream) as compared
to traditional techniques (only 5-20%) that exploit
statistical redundancy, Huffman coding, or
probability method to represent and compress
market data.

Since a thousand trades can occur between 50 +/-
milliseconds, the inexactitude in trade sequencing
would cause analytic results based on vector
measurements/ visualized heat-maps to be
erroneous. To overcome this inherent problem of
data imprecision, our suite of patented inventions
applies a “music plagiarism detection” method to
achieve higher tolerance to the unsynchronized
clock issue and is capable of recognizing patterns
more quickly (up to 50 milliseconds top speed, as
compared to taking hours or days or even months
for trade review). Aside from the accelerated
speed to decipher what’s going on in the market, it
has fewer false-positives/ false-negatives than the
traditional techniques. It makes implementation of
preventive controls in real- time possible; and
there are other benefits such as the ease of trade
reconstruction, order book replay simulation,
backstop assurance, case management
capabilities, crowd computing methods, and more.